- Cryptocurrency
- Updated On: April 6, 2026
Table of Contents
Moving crypto from one blockchain to another is more common than ever. You may do it to use a new platform, switch to a new token, or use more favorable rates. This is typically carried out with the help of a tool called a crypto bridge, an instrument that assists in moving your funds between blockchains.
It seems easy to do at first. You plug in your wallet, authorize the payment, and expect that your money will be deposited beyond the wall. It is here that most people get caught up.
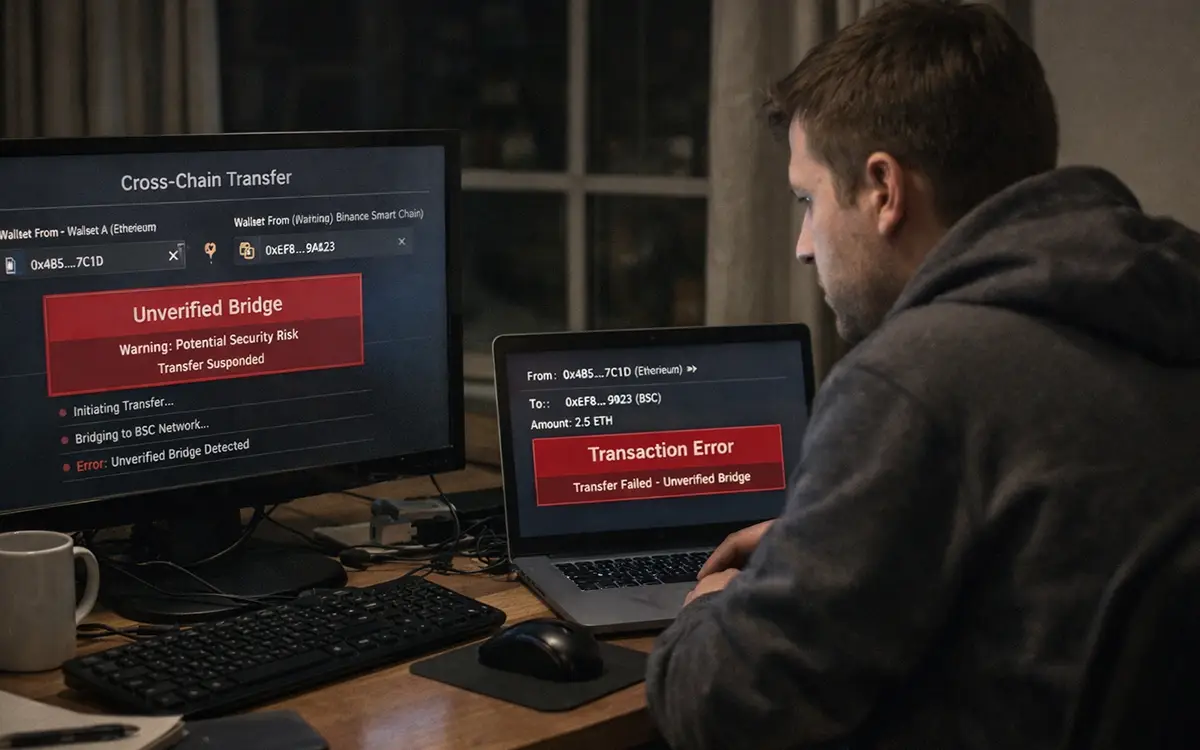
Cross-chain transfers involve more than just a single step. Multiple systems are working in the background, and that complexity creates room for mistakes and manipulation. Scammers take advantage of this exact moment when users are focused on completing a transfer and not questioning what’s happening behind the scenes.
In many cases, people don’t realize anything is wrong until their funds never arrive, or their wallet balance suddenly drops. Crypto bridge scams are designed to exploit trust and timing. A fake platform, a misleading link, or a hidden permission request can be enough to drain funds within minutes.
In this guide, you’ll learn how these scams work, why cross-chain transfers carry a higher risk, and what you can do to protect your crypto before making your next move.
What Is a Crypto Bridge?
A crypto bridge is a tool that allows you to move your crypto from one blockchain to another. Since blockchains do not naturally connect, these bridges act as the link that makes cross-chain transfers possible.
People often use them to access new platforms, explore different tokens, or take advantage of lower fees, especially when interacting with decentralized finance platforms. However, these opportunities also come with risks, similar to those seen in DeFi scams and wallet-related fraud.
Though this might look like a simple process, there is more going on behind the scenes than most users would care to know. Your money is not being transported. They will follow a sequence of processes that rely on the proper functioning of smart contracts and external systems.
Often, it goes unnoticed until one makes a payment and the money never reaches the destination, or their wallets are empty. The scams of crypto bridges are intended to play on trust and timing. In the recent data, the degree of the seriousness of the risk has been revealed. In 2025, crypto platforms lost over $3.4 billion, and the attacks on users and transactions, such as wallet access and transfers, were also growing.
The best way to observe how these risks can become real losses is to determine how crypto bridge scams operate in real transactions.
How do crypto bridge scams work?
Crypto bridge scams usually don’t look like scams at first. In most cases, the process feels normal, the interface looks familiar, the steps are the same, and nothing immediately seems wrong. The problem is that these scams are designed to blend into real transactions, making them harder to detect until the damage is already done.
Here’s how they typically happen.

-
Fake Bridge Platforms
One of the most common methods is through fake bridge websites. These platforms are designed to look almost identical to trusted services. Users land on them through ads, search results, or shared links, and everything appears legitimate.
Once the wallet is connected and the transaction is approved, the funds are sent, but not to the intended destination. Instead, they go directly to the scammer’s wallet.
-
Smart Contract Exploits
In some cases, the bridge itself may be real, but the underlying smart contract has a vulnerability. Hackers monitor these weaknesses and use them to interfere with transactions.
Funds can be drained during the transfer process or shortly after, often without any immediate warning to the user.
-
Wallet Approval Abuse
Many users don’t realize that approving a transaction can sometimes grant broader permissions. This is similar to how certain attacks, such as dusting attacks, are used to interact with wallets in ways users may not fully understand.
Once approved, they may not need further action. Funds can be withdrawn later, even if the initial transfer seemed successful.
-
Phishing During Transfers
Phishing contributes significantly to bridge fraud. Fake links can be encountered by users via emails, social media, or even sponsored ads. The links lead to malicious sites that resemble actual bridges. These tactics are commonly seen in phishing crypto scams, where attackers create near-identical platforms to trick users into revealing sensitive information or approving harmful transactions.
Since the users are interested in the transfer, they might even overlook tiny variations in the site or the URL.
In all these cases, funds are lost in a process that should be safe. The even more alarming aspect of this is that these frauds exploit the nature of cross-chain transfers, and that is why it is as important to learn about the dangers of such transactions as it is to learn about the scams.
Why Are Cross-Chain Transfers High Risk?
At a glance, cross-chain transfers feel like a routine part of using crypto. A lot of users repeat the same steps several times without any problems, and this gives them an element of familiarity and trust.
But the risk lies in what you don’t see.
Bridging, unlike simple transactions, requires several systems to interact. This increases the chances of something going wrong, especially if the platform is not secure or the process is not fully understood.
Here are the key reasons why cross-chain transfers carry a higher risk:

-
Multiple Steps Involved
A single transfer can include several processes happening in the background, increasing the chance of errors or manipulation.
-
Dependence on Third-Party Platforms
Most bridges are not built into your wallet. You rely on external platforms, which may not always be trustworthy.
-
Limited Visibility for Users
You only see part of the transaction, making it harder to detect if something is off.
-
Irreversible Transactions
Once the transfer is approved, there is no way to undo it, even if it was sent to the wrong place.
-
Easier for Scammers to Interfere
The complexity and speed of these transactions create the perfect conditions for scams to go unnoticed.
Because these risks are not always obvious, many users only recognize them after a loss has already happened. That’s why knowing the warning signs in advance is critical before making any cross-chain transfer.
Common Signs of a Crypto Bridge Scam
Crypto bridge scams are often hard to spot right now. The process can look normal, and by the time something feels off, the transaction is already complete.
That’s why it’s important to pay attention to small warning signs before and during the transfer. These signs may seem minor, but they often point to a bigger issue.
Here are some common red flags to watch for:

-
Unverified or Newly Created Websites
The platform may look legitimate, but the URL is slightly different or has been recently created. Scammers often copy real websites and rely on users not checking the details carefully.
-
Unusual Wallet Permission Requests
Instead of a simple transfer approval, the platform asks for broader access to your wallet. This can allow scammers to move funds later without your knowledge.
-
Delays Followed by Missing Funds
Transactions that take longer than expected with no clear update can be a warning sign. In some cases, funds never reach the destination at all.
-
Poor Interface or Broken Tracking
Missing transaction details, incorrect status updates, or a platform that doesn’t work smoothly can indicate a fake or poorly built bridge.
-
No Official Documentation or Support
Legitimate platforms usually provide clear information and support. If you can’t find any details or get help, it’s a risk.
These signs don’t always appear all at once, which is why they are easy to overlook. But noticing even one of them should be enough to slow down and double-check before continuing.
Real Risks Behind Crypto Bridge Hacks and Scams
The impact of a crypto bridge scam is often more serious than it appears at first. In many cases, it’s not just a failed transaction; the loss can extend beyond what you initially intended to transfer.
Here are the key risks users face:
-
Loss of Entire Wallet Balances
Some scams involve wallet permissions, not just a single transaction. This means attackers may gain access to your wallet and withdraw multiple assets, not just the amount you were transferring.
-
Difficulty Tracing Funds Across Chains
Once funds move across different blockchains and wallets, tracking them becomes complicated. Without proper tools or expertise, it can be hard to understand where the money went.
-
Limited Recovery Options
Crypto transactions are irreversible. In most cases, once the funds are gone, there is no direct way to get them back. Recovery depends on investigation and timing, and even then, it is not guaranteed. In some situations, victims are further targeted through crypto withdrawal fee scams, where fraudsters demand additional payments under the false promise of releasing or recovering funds.
-
Emotional and Financial Stress
Beyond the financial loss, there is a personal impact. Many users feel stress and confusion, especially when the transaction seemed normal at the time.
These risks are not unique to bridge scams. Similar patterns can be seen across different types of financial fraud, in which small gaps in awareness are exploited to target users. This is why taking preventive steps before making a transfer is critical.
How to Protect Yourself During Cross-Chain Transfers?
Most crypto bridge scams don’t rely on advanced hacking. They rely on small mistakes, clicking the wrong link, trusting the wrong platform, or approving something too quickly.
A few simple checks can reduce that risk significantly.

-
Verify the Website Carefully
Always use official sources or type the URL yourself. Avoid clicking links from ads, messages, or search results, as scam sites often look almost identical to real ones.
-
Use Trusted Platforms Only
Stick to well-known bridges with a credible history. If a platform is unfamiliar, take a moment to research it before using it.
-
Review Wallet Permissions Before Approving
Don’t approve requests without understanding what access you are giving. Some permissions can allow more than just a single transaction.
-
Start with a Small Test Transfer
Send a small amount first to confirm that the process works correctly before transferring larger funds.
-
Take Your Time During the Process
Avoid rushing. Most scams rely on users acting quickly without checking details. A few extra seconds can help prevent mistakes.
These steps may seem basic, but they are often enough to prevent the most common bridge-related scams.
What to Do If You Lose Funds in a Crypto Bridge Scam?
Realizing your funds are gone can feel overwhelming. The most important thing at this stage is to act quickly and avoid making decisions that could lead to further loss.
-
Stop Further Transactions
As soon as you notice an issue, stop using the bridge or interacting with the platform. Do not try to recover the funds by sending more crypto or approving additional requests. This often makes the situation worse.
-
Secure and Save All Details
Collect everything related to the transaction. This includes transaction IDs, wallet addresses, screenshots, and any links or messages you used. These details are important for understanding what happened and for any further investigation.
-
Report the Incident
Report the issue to the platform involved, if it is legitimate, and to relevant authorities or cybercrime portals. While this may not reverse the transaction, it helps create an official record and can support broader action against scams.
-
Consider Professional Investigation Support
Cross-chain transactions can be difficult to analyze without the right tools. This is where professional investigation support can help. Experts can trace the movement of funds across wallets and networks, helping you understand where your assets went and what options may exist.
Organizations like Global Financial Recovery work on analyzing blockchain activity and building clear transaction reports. This kind of insight can be useful for reporting, documentation, and exploring possible recovery paths.
When Transfers Go Wrong
Crypto bridges make it easier to move across blockchains, but that convenience comes with hidden risks. What looks like a simple transfer can involve multiple steps, systems, and permissions, and that’s exactly where things can go wrong.
Most bridge scams don’t rely on complex tricks. They work because the process feels routine. Even a friendly interface, a swift approval, and a little bit of trust may result in a tremendous loss.
The intention is not to stop using bridges but to use them consciously. Mistakes that may be hard to undo can be avoided by taking a few extra seconds to check a platform or check permissions.
And if something doesn’t feel right before or after a transaction, having clarity matters.
To the few of you who are confused about a suspicious transaction or simply want to know where your money went, experts such as Global Financial Recovery can help break down the activity, and the resulting picture is much clearer, so you can decide your next steps with confidence.
FAQs (Frequently Asked Questions)
A crypto bridge scam happens when a user tries to transfer assets between blockchains using a fake or compromised platform. This can involve phishing websites, malicious smart contracts, or hidden wallet permissions. During cross-chain transfers, users are more vulnerable because the process involves multiple steps, making it easier for scammers to interfere without being noticed.
Hackers drain funds by exploiting weak points in the transfer process. This can include redirecting users to fake bridge websites, tricking them into approving harmful wallet permissions, or taking advantage of vulnerabilities in smart contracts. In some cases, users believe the transfer is successful, but the funds are sent to a scammer’s wallet instead.
Common warning signs include slightly different website URLs, poor interface design, missing transaction details, and a lack of official documentation or support. Users may also be asked for unusual wallet permissions. If a platform feels unfamiliar or incomplete, it’s important to verify it before proceeding.
In most cases, crypto transactions cannot be reversed once completed. However, it may be possible to trace the movement of funds through blockchain investigation. This can help identify where the assets were transferred and support reporting or further action, although recovery is not guaranteed.
To reduce risk, always use trusted bridge platforms, verify URLs carefully, and avoid clicking links from ads or messages. Review wallet permissions before approving any transaction and consider starting with a small test transfer. Taking a few extra steps can help prevent costly mistakes during cross-chain transfers.




