
- Cryptocurrency
- Updated On: April 27, 2026
Table of Contents
In recent years, the crypto market has been exploding, and even those who had no prior knowledge about it are now showing a keen interest. The fact that the crypto market has shown strong potential to generate substantial returns has garnered a lot of attention, even from those who initially thought it was just hype.
However, those who invest in the crypto market do not have enough knowledge and end up losing their money to cyber threats. According to the Chainalysis 2026 Crypto Crime Report, approximately $17 billion was stolen in cryptocurrency scams and fraud in 2025.
Moreover, cryptocurrency wallets are garnering a lot of attention in recent times as the number of fake crypto brokers and exchanges is increasing at a high rate.
Losing your crypto to online fraud can be mentally and financially devastating. Also, it would be too late to blame them for the loss, which could have been easily avoided if the proper precautions had been taken.
Thus, securing these cryptos is important, and this article will explain why. It is for you regardless of whether you already have experience in the crypto market or are a newbie. We will take a deep dive to understand the importance and to differentiate between genuine and fake crypto wallets.
Understanding Fake Crypto Wallet Scams
A fake crypto wallet is a fraudulent application, device, or online service created to steal funds from users. Scammers use different techniques to trick victims into giving up control over their digital assets, including:
- Fake Wallet Apps: Malicious apps designed to look like real wallets, prompting users to deposit funds
- Phishing Websites: Fake sites that mimic legitimate wallets, stealing login credentials
- Trojanized Wallets: Wallets that contain hidden malware, allowing remote access to funds
- Fake Customer Support Scams: Impersonating official wallet providers to manipulate users into revealing sensitive data
Many scams rely on social engineering, where fraudsters gain victims’ trust through fake social media profiles, deepfake influencer videos, or Telegram groups promoting fraudulent wallet services.
How Fake Crypto Wallet Scams Work?

Scammers use various tactics to deceive crypto users. Some of the most common methods include fraudulent wallet apps that appear on app stores with fake positive reviews, phishing attacks where scammers send emails or messages with fake login pages tricking users into entering their credentials, and fake customer support where fraudsters pose as official representatives convincing victims to share private keys.
Some fake wallets contain malware that allows scammers to access victims' funds remotely. Social media and online ads are also used to promote fraudulent wallets, leading unsuspecting users to download and use them. Once scammers gain access to a victim’s wallet, funds are immediately transferred to scam-controlled addresses, making recovery nearly impossible.
Where Fake Crypto Wallets Are Distributed?
These fraudulent wallets are aggressively promoted across various online platforms. Fake apps disguised as real wallets appear on Google Play & Apple App Store, phishing websites mimic legitimate wallets, and fraudulent promotions on Facebook, Instagram, and YouTube lure victims.
Scammers use Telegram and Discord groups to promote scam "airdrop wallets" that ask for deposits, while fake search engine results lead to phishing links. Deepfake influencer scams also play a role in tricking users into downloading fake wallets.
Red Flags: How to Identify a Fake Crypto Wallet
Fake wallets can be hard to detect, but some warning signs indicate a potential scam. If a wallet has no official website or verified developer information, requests private keys or seed phrases during setup, asks for excessive permissions like access to contacts or cameras, or has suspiciously high ratings with fake positive reviews, it is likely fraudulent.
A legitimate wallet provider will never ask for private keys, and any service requesting them should be treated as a scam.
Table: Fake vs. Legitimate Crypto Wallets
|
Feature |
Fake Crypto Wallet |
Legitimate Crypto Wallet |
|
Source of Download |
Hosted on phishing websites, fake app stores, or unknown third-party links. |
Available only on official wallet websites, Apple App Store, or Google Play Store. |
|
Security & Verification |
No official security audits or open-source verification. |
Transparent code, open-source, and verified security audits from third-party experts. |
|
Permissions Requested |
Requests unnecessary access, such as contacts, microphone, or camera. |
Requests only relevant permissions needed for crypto transactions. |
|
Customer Support |
No legitimate support or redirects users to phishing sites. |
Has official customer support channels with verified contact details. |
|
Private Key or Seed Phrase Request |
Asks for seed phrases or private keys during setup. |
Never asks for private keys or seed phrases. |
|
Reviews & Reputation
|
Fake or minimal user reviews, often inflated ratings. |
Has a long-standing reputation with real user feedback on forums like Reddit and BitcoinTalk. |
Real-World Case of Fake Crypto Wallet Scams
Scammers created a fake trust wallet app on Google Play; this app was so deviously created that it resembled the original Trust Wallet. This fake crypto wallet also had fake reviews of the app, which further enticed crypto users to download this app.
After downloading this fake app, the app prompted its users to provide their private key details under the fake assurance to recover their cryptos in case of restoring the wallet. These details were sent directly to the scammers.
For a while, this wallet allowed its victims to carry out transactions, but later, it started sending their cryptos directly to the scammer's wallet.
Why Fake Crypto Wallet Scam is Popular?
The Google Play Store hosted both the original Trust Wallet and a fake one. Due to the deceptive tactics of scammers, including fake reviews of the site, which further boosted its popularity and rank ahead of the original one.
The other reason for the popularity of this fake crypto wallet was through social engineering. It was promoted on email and social media platforms.
Can Funds Lost to Fake Crypto Wallets Be Recovered?
In some cases, recovery may be possible but it is rarely straightforward.
Cryptocurrency transactions are designed to be irreversible, and once funds are moved through multiple wallets or converted across chains, tracing becomes more complex. Unlike traditional banking systems, there is no central authority that can reverse a transaction on request. This is one reason why victims of crypto withdrawal fee scams and fake investment platforms often struggle to recover funds once transfers are completed.
That said, outcomes often depend on a few key factors:
- How quickly action is taken
Early analysis improves the chances of tracking fund movement before it becomes too fragmented. - Whether the funds have been further transferred or withdrawn
The more layers added, the harder it becomes to follow the trail. - Availability of transaction data and wallet details
Clear records significantly improve the ability to investigate.
While recovery is not guaranteed, timely and informed action can make a meaningful difference in certain cases.
How to Avoid Fake Crypto Wallet Scams?
Let’s discuss the tips to avoid fake crypto wallet scams.

1. Download Wallets Only from Official Sources
- Always visit the official website of a crypto wallet provider to find download links.
- Cross-check app reviews, ratings, and developer information before installation.
2. Enable Two-Factor Authentication (2FA)
- Activate 2FA on wallets and exchange accounts for an added layer of security.
- Avoid using SMS-based 2FA, as SIM swapping attacks can bypass it.
3. Never Share Private Keys or Seed Phrases
- Store private keys offline in a secure location, such as a hardware wallet or written note.
- If a wallet provider asks for your seed phrase, it's a scam, report it immediately.
4. Use a Hardware Wallet for Large Crypto Holdings
- Hardware wallets like Ledger and Trezor provide better security by keeping private keys offline.
- Always purchase hardware wallets directly from the manufacturer's website.
5. Beware of Crypto Giveaway Scams
- If it sounds too good to be true, it probably is.
- Avoid offers that promise free cryptocurrency in exchange for deposits or personal information.
6. Regularly Update Wallet Software
- Keep wallet apps updated to ensure security patches are applied.
- Avoid using outdated software versions that may have vulnerabilities.
By recognizing red flags and following security best practices, users can significantly reduce the risk of falling victim to fake crypto wallet scams. Staying vigilant and skeptical of unsolicited crypto offers is key to safeguarding digital assets in the ever-evolving crypto landscape.
Also, check out our detailed guide on How to Choose the Right Crypto Wallet.
What Not to Do If You’ve Used a Fake Crypto Wallet
Realizing a wallet may be fake can trigger panic. In that moment, certain actions can make the situation worse or reduce any remaining chances of tracing funds.

Here are some common mistakes to avoid:
-
Do not send additional funds to “unlock” or “recover” your balance
Scammers often request extra payments under the guise of withdrawal fees, taxes, or verification charges. These are almost always fraudulent. -
Do not trust recovery promises from unknown third parties
After initial losses, victims are often targeted again by so-called “recovery agents.” If they guarantee results or ask for upfront fees without verification, it’s a red flag. -
Do not delay documenting transactions
Wallet addresses, transaction IDs, emails, and platform links are critical. Losing access to this information can make tracing significantly harder. -
Do not continue interacting with the scam platform
Any further engagement gives scammers more opportunities to manipulate or extract information. -
Do not assume the funds are immediately recoverable
Acting on false hope can lead to rushed decisions, including falling into secondary scams.
What to Do If You Fall Victim to a Fake Wallet Scam
If you suspect that your funds have been compromised, the focus should shift to securing information and assessing what can still be tracked.
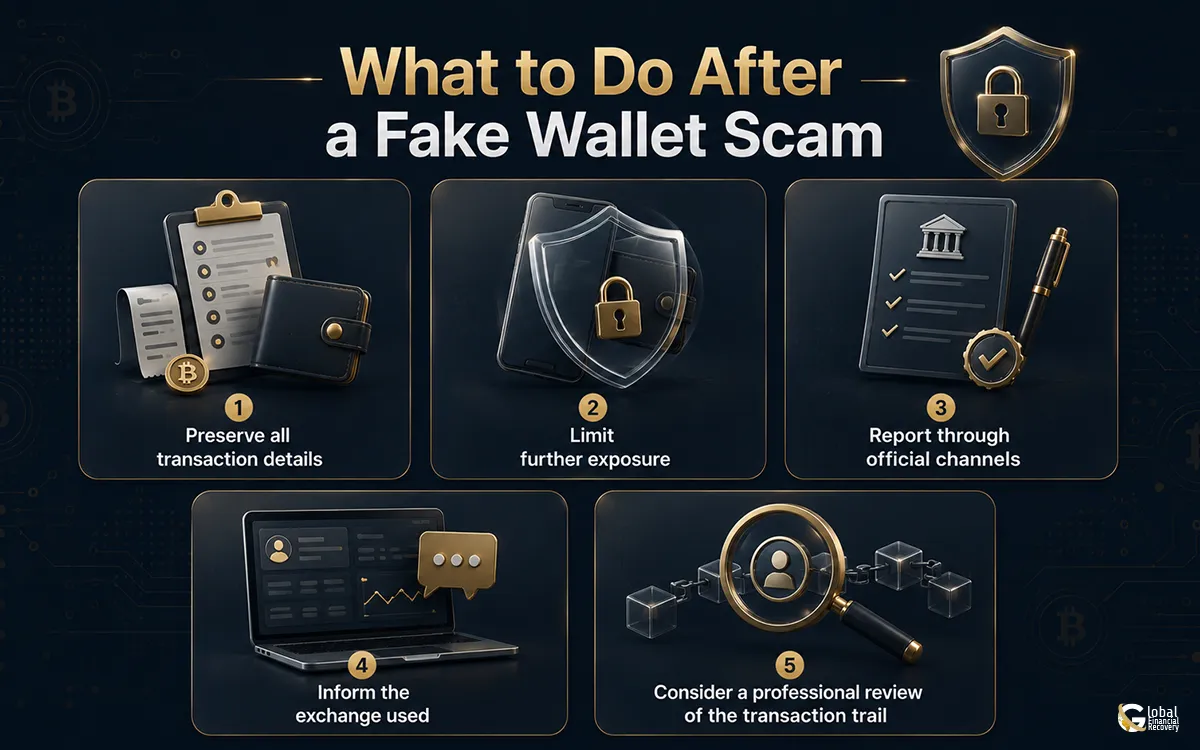
Preserve all transaction details
Save wallet addresses, transaction IDs, emails, and any platform links involved.
Limit further exposure
Disconnect wallets from suspicious platforms and avoid additional interactions.
Report through official channels
This may include agencies such as IC3, FTC, or relevant local cybercrime authorities, depending on your location.
Inform the exchange used (if applicable)
In some cases, early reporting may help flag suspicious activity.
Consider a professional review of the transaction trail
Understanding how funds moved can help determine whether any recovery path exists.
While crypto transactions are often difficult to recover, early and structured action can help preserve what options may still be available.
Before You Trust a Wallet, Remember This
Fake crypto wallet scams succeed by appearing legitimate. Understanding how they work, recognizing red flags, and choosing verified wallets are essential to avoiding them. When exposure has already happened, speed and clarity matter — preserving transaction details, avoiding additional payments, and limiting further interaction can influence what remains possible.
For those who are unsure about their situation or want a clearer understanding of what can realistically be done, it may help to have your case looked at with a structured approach.
Global Financial Recovery works with individuals dealing with crypto-related fraud, focusing on tracing transactions and evaluating possible recovery paths based on real data, not assumptions.
You can explore your options and decide what makes sense for your situation from there.
FAQs (Frequently Asked Questions)
These create a fraud or phishing application or website that traps a user to provide log-in details and use them to empty funds from the user's account.
Search the official website, developer performance, and reviews from reputable sources. It is forbidden to download wallets from unverified sources.
Recovery is difficult, but reporting the scam to authorities, notifying the cryptocurrency exchange, and using blockchain forensics increase the chance of retrieval.
Yes, they are. Hardware wallets store private keys offline, providing additional protection from hacking and fraud over the internet.




