- Cryptocurrency
- Updated On: March 10, 2026
Table of Contents
A new Layer-2 blockchain project is usually introduced with a strong brand, vague technical statements, and increasing online momentum. The offer is appealing: it claims to be faster and cheaper, and it will launch sooner than many people think. This could be the next significant upgrade in crypto infrastructure. To investors and common users, it may seem like a chance that cannot be missed.
This is, however, the beginning of the risk. False Layer-2 frauds grow more common as they are being implemented on top of legitimate innovations. As actual Layer-2 networks strive to enhance scalability, criminals create convincing simulations that appear just as credible on the surface.
They encourage presales, airdrops, and exclusive early-access activities aimed at generating urgency. Later, when many victims are questioned, they say that they thought they were dealing with an authentic blockchain launch.
It is not merely the technical complexity that can be the actual threat, but a false sense of security at the time of excitement. With the growing adoption of blockchain, the number of people seeking to leverage it is also increasing. In this blog, we are going to dissect how counterfeit Layer-2 scams work, why they can steal millions of dollars, and what you can actually do to secure your crypto assets against being victims of fake Layer-2 schemes.
What Are Layer-2 Networks?
Blockchains make use of layer-2 networks to make them cheaper and faster to operate. Indicatively, the Ethereum-based network is being utilized to minimize congestion and cut down on transaction expenses. Rather than executing all transactions on the primary blockchain, Layer-2 protocols do their business independently and store the end outcome on the primary network.
You can read about such terms as "optimistic rollups" and "zk-rollups." These are simply different methods used to confirm transactions efficiently. The technical process is sometimes complex in nature, yet the aim is to enhance speed, cut costs, and serve more users.
The layer-2 projects are usually of high interest because they are linked to major blockchains. Investors are interested in such indicators as increasing users and total value locked (TVL) when a new network is being launched, as it demonstrates the amount of crypto being deposited in the network.
Real projects are not secretive regarding their team, technology, and audits. Counterfeit projects imitate the words and style but do not have any substance. This difference should be understood before believing anything new.
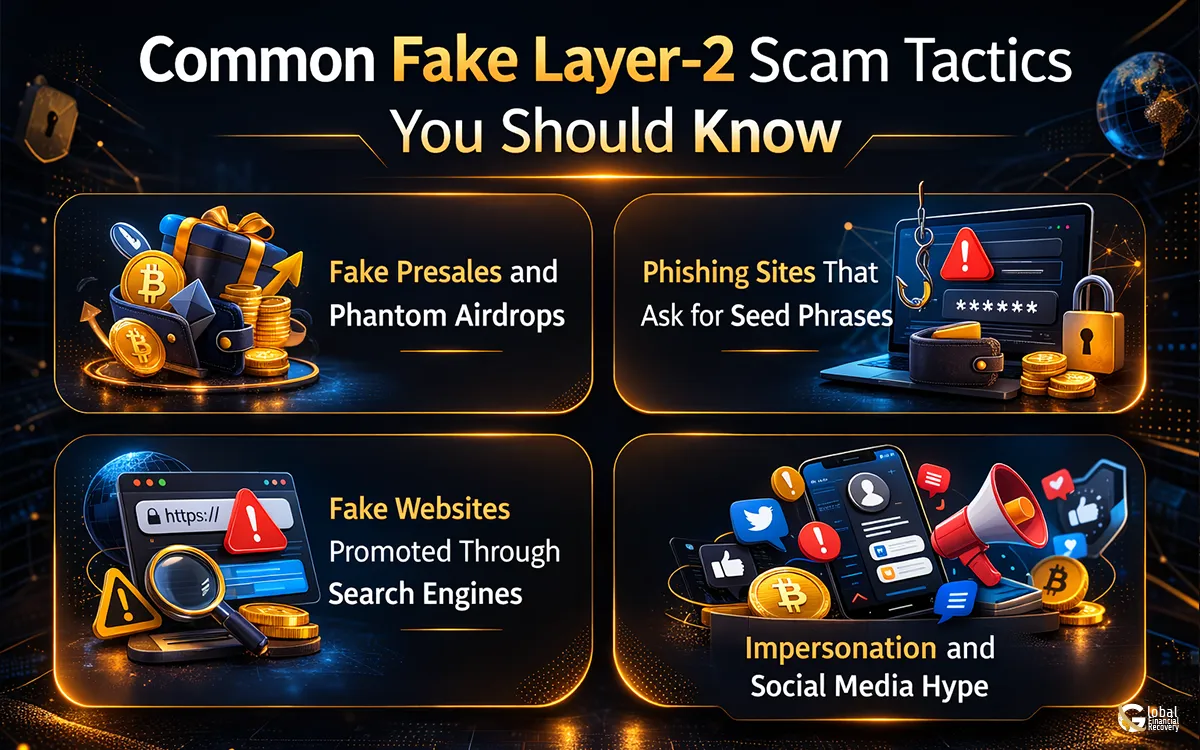
Common Fake Layer-2 Scam Tactics You Should Know
As Layer-2 projects gain attention, scammers copy the same playbook again and again. The methods may look different on the surface, but the goal is always the same: get you to connect your wallet, approve a transaction, or share sensitive information.
Here are the most common tactics being used today:
1. Fake Presales and Phantom Airdrops
Scammers create websites that look like official Layer-2 launches. They promote early token presales or “exclusive” airdrops. Users are asked to connect their wallets to claim tokens or secure early access.
Instead of receiving tokens, victims unknowingly sign malicious approvals. Within minutes, funds are transferred out of their wallets.
2. Phishing Sites That Ask for Seed Phrases
Some fake Layer-2 platforms claim users must “verify” or “sync” their wallet before participating. The site then asks for a recovery phrase or private key.
No legitimate blockchain project will ever request your seed phrase. Once shared, attackers gain full control of the wallet and can drain all assets.
3. Fake Websites Promoted Through Search Engines
Criminals also promote fake Layer-2 networks through paid search ads and manipulated search results. A user searching for a legitimate project may click on the first result, assuming it is official.
The website may look professional, but it is designed to capture wallet approvals or redirect funds to scam addresses.
4. Impersonation and Social Media Hype
Fraudsters create fake accounts that imitate developers, founders, or community managers. These impersonators join crypto groups, comment on posts, and share links to fraudulent presales.
The activity creates artificial credibility. When multiple accounts repeat the same message, it feels real even when it is not.
Understanding these tactics is important because fake Layer-2 scams rarely look suspicious at first glance. They are designed to blend into legitimate blockchain growth and take advantage of trust during high-interest periods.
Why Layer-2 Hype Makes Investors More Vulnerable?
A Layer-2 technology is usually promoted as the next phase of blockchain development. New projects are announced, the number of media reports is growing, discussions on social media increase rapidly, and investors start paying attention to the topic. When the adoption rates and the funds are highlighted in the news, the users firmly believe that the space is secure and properly monitored. Regrettably, fast growth is also the best place to commit fraud.
Layer-2 systems are not completely known to the majority of investors. They can be aware of a large blockchain name, but they can hardly prove that the new project is not something secret. It is this lack of knowledge on the part of the scammers that the scammers count on. They produce the impression of credibility with references to the known ecosystems, use of technical language, and a reference to professional branding, which is believable.
Another obvious trend exists as well, namely, the more Layer-2 is adopted, the more phishing attacks and attempts at scams are likely to appear. Criminals follow attention. In case of seeking new token sales, bridge services, and early airdrops, scammers place fake sites in the same locations.
Other than technology, there is a significant role in psychology. Urgency and exclusivity are methods of urgency that are used to push quick decisions by the fraudsters. Terms such as "limited presale," "early access," or "exclusive rewards" are meant to cause the feeling of missing out. Investors have a weak tendency to check out the details when they believe that they need to do something fast, and that is when errors can occur.
Real Consequences: Millions Lost to Fake Layer-2 Scams
Fake Layer-2 scams and related phishing attacks are costing real investors significant sums. In January 2026, crypto scams and exploits, largely driven by phishing, wallet drainers, and impersonation attacks, resulted in over $370 million in total losses across blockchain networks.
A large portion of that came from fraudulent online ads and fake sites impersonating legitimate DeFi platforms, where victims were tricked into connecting wallets and approving malicious transactions. One reported individual lost hundreds of thousands of dollars after interacting with a counterfeit site that appeared at the top of search results, mimicking a trusted platform’s interface.
These losses highlight a broader trend: scammers don’t need to exploit a protocol vulnerability to steal funds; they only need to trick a user into approving. Once a wallet signs a transaction or permit for a malicious address, attackers can drain assets almost instantly.
Once funds are moved out of a wallet on a blockchain, there is no central authority that can reverse the transfer. This immutability is a core feature of blockchain technology, but it also means that stolen assets are extremely difficult to recover unless specialists can trace and intervene early.
How to Spot, Avoid & Protect Yourself From Fake Layer-2 Scams?
As Layer-2 projects continue to gain attention, scammers are becoming more refined in how they approach victims. The difference between a legitimate opportunity and a fraudulent scheme is not always obvious at first glance. Protecting yourself requires patience, verification, and a clear understanding of common warning signs.
-
Verify Official Sources
Always ensure that any interaction that involves any Layer-2 project is legitimate. Authentic projects use similar branding on their website, documentation, and official community outlets. They release audit reports and technical and development updates that can be reviewed independently. In case the team, roadmap, or smart contracts are not clear or not provided, then it is a cause for concern.
-
Watch out when You Want to attach your wallet
There are a lot of counterfeit Layer-2 frauds that do not require seed phrases anymore. They instead demand a wallet connection and a simple signature. It is a silent accord that is capable of giving the go-ahead to transfer tokens or gain entry to assets. Do not hook up your wallet if you do not trust it fully on a platform. A single slip of the approval may lead to instant loss.
-
Look at the Website Addresses Carefully
Fake websites are almost similar to genuine websites. The variation can be one or two spelling differences or a domain extension. It is always a good idea to look at the entire web address and never to visit a link given in an unsolicited message or advertisement. Get online through verified sources when in need.
-
Additional Protection by use of Security Tools
Current wallets and security systems provide a warning message prior to the authorization of a risky transaction. Some tools examine smart contracts and alert to suspicious activity. Although the tools do not ensure safety, they offer an added protection in the process of venturing into new projects.
-
Do Not Act on Hype Alone
One of the best tools of scammers is urgency. Premeditated sales, countdown timers, and exclusive reward offers are meant to coerce snap-on purchases. Authorized Layer-2 initiatives can resist scrutiny. When you are in a hurry, stop and check before moving on.
Protecting your crypto assets is not about avoiding innovation; it is about approaching it responsibly. A few extra minutes of verification can prevent permanent financial loss in an environment where transactions cannot be reversed.
What to Do If You’ve Been Scammed?
Falling victim to a fake Layer-2 scam can feel overwhelming, but structured action is critical. The steps you take in the first few hours can directly impact whether funds can be traced or further losses prevented.
-
Secure Your Wallet Immediately
Stop interacting with the suspicious platform at once. Disconnect your wallet and revoke any token approvals that may have been granted. If there are remaining assets, transfer them to a newly created wallet with a fresh private key. This reduces the risk of additional unauthorized transactions.
-
Preserve All Transaction Evidence
Document everything related to the incident. Save transaction hashes, wallet addresses, screenshots of the website, confirmation messages, and any communication you received. Blockchain investigations rely heavily on accurate data. The more information preserved, the stronger the tracing process can be. It can also help to understand how similar fraud schemes operate. Reviewing patterns explained in resources such as DeFi scams and DeFi wallet scams can provide insight into how attackers misuse smart contract approvals and wallet permissions.
-
Seek Professional Blockchain Investigation Support
Blockchain transactions are transparent but complex. While transfers cannot simply be reversed, stolen funds can sometimes be traced as they move across wallets and exchanges. Professional recovery services, including structured cryptocurrency scam recovery support, focus on forensic blockchain analysis and coordination with exchanges when possible.
Organizations such as Global Financial Recovery work with investigators and legal channels to assess potential recovery pathways. Although recovery is never guaranteed, early intervention significantly increases the possibility of tracing and containing stolen assets.
Taking immediate, informed action is the most effective response after a scam. Delay often allows funds to be further dispersed, making recovery more difficult.
Protect Your Crypto With Clarity and Action
Layer-2 networks are advancing blockchain technology, but the rapid growth around them has also created new opportunities for fraud. Fake projects are increasingly sophisticated, using professional branding and urgency to mislead investors. Once a transaction is confirmed on the blockchain, it cannot be reversed. That reality makes prevention and decisive action essential.
When exposure to a fraudulent Layer-2 platform occurs, immediate steps matter. Secure the wallet, revoke approvals, preserve transaction records, and stop further interaction with the suspicious site. Acting quickly strengthens the ability to trace fund movements and limit additional loss.
A professional blockchain investigation provides a structured analysis of wallet activity and fund flows. Global Financial Recovery works with forensic specialists to trace transactions and assess realistic recovery pathways based on verifiable data. If you believe you may have interacted with a fraudulent platform, you cancontact the recovery specialists to discuss the situation and explore the next steps.
Blockchain innovation should deliver progress, not preventable losses. Careful verification, informed decisions, and prompt professional support remain the strongest safeguards in an evolving crypto environment.
FAQs (Frequently Asked Questions)
Scammers often fabricate on-chain credibility by displaying inflated “total value locked” (TVL), fake wallet activity, or copied transaction dashboards. Some even deploy simple smart contracts to simulate activity. Always verify metrics through independent blockchain explorers and trusted analytics platforms rather than relying on figures shown on the project’s own website.
Yes. Certain token approvals grant unlimited spending permissions to a contract address. If that address is controlled by attackers, they can transfer tokens at any time without further consent. Revoking unused approvals regularly is a critical security practice in decentralized finance.
Warning signs include anonymous bridge operators, no published audit reports, unclear validator mechanisms, unrealistic transaction speed claims, and pressure to move funds quickly. Legitimate Layer-2 bridges provide transparent documentation explaining how assets are locked, validated, and released.
Fraudsters purchase paid advertisements targeting trending blockchain keywords. These ads often appear above legitimate results and use nearly identical domain names. Because users trust search rankings, they may click without verifying the URL carefully, leading directly to phishing interfaces designed to capture wallet approvals.
Blockchain transactions are publicly recorded, which allows forensic analysts to track fund movements across wallets and exchanges. However, attackers often use mixers, bridges, and rapid transfers to complicate tracing. Immediate investigation significantly improves the ability to identify fund flows and potential recovery pathways.