
- Cryptocurrency
- Updated On: March 11, 2026
Table of Contents
Crypto money mule scams are quietly pulling ordinary people into serious financial trouble, often without them realizing anything is wrong. These scams usually appear as harmless work-from-home jobs, easy crypto tasks, or simple requests to move funds, which is why so many people fall for them.
Criminals are placing their stolen crypto into different wallets and platforms using victims as go-betweens behind the scenes. This assists in concealing the real source of money. When the victims are aware of what is occurring, the wallets might be flagged, accounts limited, or transactions attached to an investigation.
The fact that these scams closely resemble other types of crypto fraud, including so-called fake crypto wallet scams, where users are duped into using wallets monitored or controlled by criminals, makes them particularly dangerous. The moment money enters the wallet of a victim, the legal and financial risk is usually on the victim, not the fraudster.
This guide explains how crypto money mule scams work, how victims are recruited, the warning signs to watch for, and what to do if you believe you’ve already been involved.
What Is a Money Mule in Crypto?
A money mule in crypto is someone who unknowingly moves stolen cryptocurrency for scammers. Instead of transferring illegal funds themselves, criminals pass the job to real people, using their wallets or exchange accounts to make the activity appear normal.
In traditional scams, money mules move money through bank accounts. In crypto scams, the process is digital, but the goal is the same. Victims may be asked to receive crypto, send it to another wallet, convert tokens, or withdraw funds through an exchange. Each transfer puts more distance between the stolen crypto and the original crime.
The most dangerous thing is that the majority of people are unaware that something is wrong in the beginning. Fraudsters tend to frame the deal as a standard business operation, temporary help, or even as a part of a valid opportunity. Cryptocurrencies travel at such speed, and all the processes are performed through the Internet, that it is easy to overlook warning signals.
Simply put, a crypto money mule is not the person behind the scam. More often, it’s a regular individual who was misled into moving stolen funds while unknowingly taking on the legal and financial risk meant for the criminals.
Now, the next section can explain exactly how crypto money mule scams work step by step, or we can move straight into how people are recruited into these roles.
How Crypto Money Mule Scams Work?
Crypto money mule scams usually follow a structured process. While the story may vary, the underlying steps are largely the same. Victims are recruited, guided through transactions, and exposed to risk once the funds are traced.

Step 1: Recruitment
Scammers contact potential victims through job listings, social media, messaging apps, or online communities. The offer often involves simple tasks, flexible work, or assistance with crypto transactions. The goal is to appear legitimate and low risk.
Step 2: Trust Building
Before requesting any transfers, scammers establish credibility. This may include professional language, fake company names, screenshots, or consistent communication. In some cases, emotional pressure or personal relationships are used to increase trust.
Step 3: Account Use or Setup
Victims are asked to use their existing crypto wallets or exchange accounts or to open new ones for “business” or “client” purposes. All activity remains in the victim’s name, even when scammers guide the process.
Step 4: Receipt of Stolen Funds
Cryptocurrency linked to scams, theft, or fraud is sent into the victim’s wallet. The transfer is often described as a payment, investment return, or temporary holding request to disguise its true origin.
Step 5: Movement and Layering
Victims are instructed to quickly forward the funds. This may involve multiple wallet-to-wallet transfers, token swaps, or withdrawals through exchanges. These steps are used to break transaction trails and delay detection.
Step 6: Discovery and Consequences
Eventually, unusual transaction patterns are flagged by exchanges or monitoring systems. Accounts may be restricted, funds frozen, and explanations requested. At this stage, the scammer disappears, leaving the victim responsible for responding to investigations.
Understanding how crypto money mule scams work step by step helps victims take action faster if they’ve already been targeted.
Why Scammers Use Money Mules Instead of Their Own Wallets?
Criminals don’t use their own crypto wallets because doing so would expose them too quickly. Instead, they rely on money mules, real people with legitimate identities, to move stolen crypto for them and absorb the risk.
Here’s why this tactic works so well for scammers:
-
It hides the real criminals
When stolen crypto moves through a victim’s wallet or exchange account, it creates distance between the crime and the people who planned it. This makes investigations slower and more complex.
-
Mule accounts appear legitimate
Wallets and exchange accounts linked to real individuals don’t raise immediate suspicion. This allows scammers to move funds through platforms that would normally block high-risk or anonymous wallets.
-
It helps bypass security checks
Exchanges and banks monitor patterns. By using many different mules and smaller transfers, criminals make illegal activity look like normal user behavior.
-
Risk is spread across multiple victims
Instead of relying on one wallet that could be shut down, scammers use many people. If one account is frozen, the operation can continue through others.
-
Manipulation is easier than hacking
Convincing someone to move crypto is often easier than breaking through security systems. Social engineering is cheaper, faster, and less risky for criminals.
-
Scammers can disappear easily
Once the funds are moved, criminals vanish. When questions arise, it’s the mule’s account, not the scammer's, that gets flagged first.
In short, money mules act as buffers between stolen crypto and the people who stole it. The criminals stay hidden, while victims are left dealing with frozen accounts, lost funds, and serious stress.
Understanding why criminals use money mules makes one thing clear: if someone asks you to move crypto for them, the risk almost always falls on you, not them.
Common Ways Victims Are Recruited as Crypto Money Mules
Crypto money mule scams rarely begin with obvious warning signs. In most cases, victims are recruited through everyday situations that appear legitimate at first.
The table below outlines the most common recruitment methods and how scammers persuade individuals to move stolen crypto on their behalf.
|
Recruitment Method |
How the Scam Starts |
What Scammers Ask Victims to Do |
Why It Works on Victims |
|
Victims see job ads or are contacted by “recruiters” offering remote crypto roles such as payment processor or account manager. |
Receive crypto payments, move funds between wallets, or convert crypto for “company operations.” |
The job sounds professional, low-effort, and well-paid, making it easy to trust. |
|
|
Victims are introduced to polished dashboards that show fake profits and trading activity. |
Transfer crypto between wallets to “unlock profits” or “verify accounts.” |
Visual dashboards create false legitimacy and urgency. |
|
|
A scammer builds an emotional bond through dating apps or social media before mentioning crypto. |
Move or hold crypto as a “temporary favor” or emergency request. |
Emotional attachment lowers skepticism and increases compliance. |
|
|
Scammers hijack or mimic social media accounts of friends or businesses. |
Quickly transfer crypto to a “safe” or “new” wallet. |
Familiar names create instant trust and urgency. |
|
|
Victims searching for help after a loss are contacted by “recovery agents” or “support teams.” |
Move crypto to “secure wallets” for tracing or recovery. |
Victims are already distressed and looking for solutions. |
|
|
Victims join crypto trading groups promising insider tips or guaranteed returns. |
Act as an intermediary to move crypto during “high-profit windows.” |
Group pressure and authority figures reduce independent thinking. |
While these approaches may look different on the surface, they all follow the same pattern: build trust first, then introduce the transfer request. Once you understand how victims are recruited, the next step is identifying the warning signs that indicate something is wrong.
Red Flags That Signal a Crypto Money Mule Scam
Crypto money mule scams are carefully designed to feel normal at first. The warning signs often appear small and harmless, which is why so many victims miss them. Below are the most common red flags.
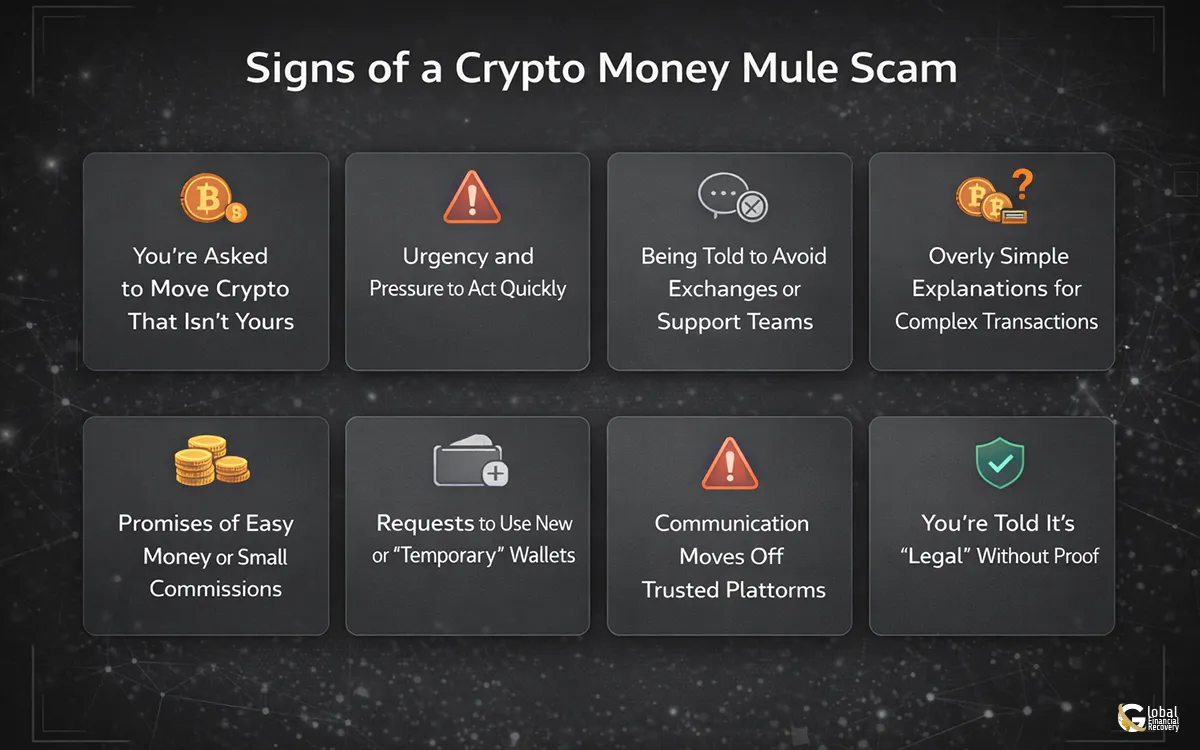
-
You’re Asked to Move Crypto That Isn’t Yours
One of the strongest warning signs is being asked to receive or transfer cryptocurrency on behalf of someone else. Legitimate jobs, investments, or relationships do not require you to move funds through your personal wallet. If the crypto doesn’t belong to you, and you’re asked to act as a middleman, that’s a major risk indicator.
-
Urgency and Pressure to Act Quickly
Scammers often push victims to act fast with "do this now,” “don’t wait,” or “the window will close.” This urgency is intentional. Speed reduces the chance you’ll question the request or seek advice. In crypto money mule scams, fast transfers help criminals break transaction trails before red flags are raised.
-
Being Told to Avoid Exchanges or Support Teams
If someone tells you not to contact an exchange, avoid customer support, or keep the transaction private, that’s a serious red flag. Scammers know that exchanges and blockchain platforms can detect suspicious activity. Isolation protects the scamnot you.
-
Overly Simple Explanations for Complex Transactions
Criminals often downplay risk with phrases like:
- “This is just routine crypto movement”
- “Everyone in crypto does this”
- “It’s how profits are unlocked”
In reality, legitimate crypto operations don’t rely on vague explanations. If the process doesn’t fully make sense, that confusion is often intentional.
Promises of Easy Money or Small Commissions
Many victims are offered a percentage, commission, or bonus just for moving crypto. The task sounds easy and low-risk, which lowers suspicion. But being paid to move funds is exactly how money mule schemes operate, both in crypto and traditional finance.
-
Requests to Use New or “Temporary” Wallets
Scammers may ask you to create a new wallet, use a specific app, or move funds through multiple wallets. These extra steps are meant to distance stolen crypto from the original crime. Legitimate businesses do not ask individuals to create wallets solely for fund transfers.
-
Communication Moves Off Trusted Platforms
Scams often shift conversations away from professional platforms to encrypted or private messaging apps. Once communication moves off-platform, scammers gain control and reduce accountability. This is especially common in job-based and romance-related crypto money mule scams.
-
You’re Told It’s “Legal” Without Proof
One of the popular reassurance methods is continuous assertion that the process is legal, with no documents, contracts, or verifiable details about the company. The legitimate operations do not depend on verbal reassurance. When it is stressed that it is legal, but it cannot be proved, then there is a need to be on the alert.
The majority of crypto money mule victims are unaware of what is going on until there is a freeze of wallets or a flagging of transactions. These red flags are easily noticed at the initial stage and can help avoid monetary loss, legal stress, and complications in the long term.
Risks and Consequences of Being a Crypto Money Mule
Even if you were tricked or didn’t realize what was happening, being used as a crypto money mule can still lead to serious problems. Scammers design these schemes so the risk falls on the victim, not on them.

- Account freezes: Banks and crypto exchanges may freeze your accounts without warning while they investigate suspicious activity.
- Loss of funds: Any stolen crypto that passed through your account can be taken back, even if you didn’t know it was stolen.
- Investigations and questioning: You may be contacted by banks, exchanges, or authorities and asked to explain your transactions.
- Permanent account closures: Some victims lose access to banking or exchange services long-term and are labeled “high risk.”
- Financial and emotional stress: Frozen funds, missed payments, anxiety, and fear are common outcomes for victims.
The key takeaway is that acting quickly matters. Stopping transactions and seeking help early can reduce damage and protect you from further risk.
If you want, the next section can explain how recovery experts can help.
What to Do If You’ve Already Been Used as a Crypto Money Mule?
If you believe you’ve been used as a crypto money mule, act quickly. Delays can increase both financial and legal risk.
First, stop all crypto activity immediately. Do not send, receive, or move any more funds, even if you’re pressured to make “one last transfer.”
Next, save all evidence. Keep messages, emails, wallet addresses, transaction IDs, and screenshots. This information is important for explaining what happened and showing that you were misled.
If your wallet or exchange account is frozen, don’t panic and don’t ignore it. Respond honestly to any requests and provide accurate information.
Finally, seek professional crypto recovery guidance. Specialists can review your case, document the situation properly, and help reduce further risk. While past transfers can’t be undone, fast and informed action can make a real difference.
Take Action Before the Damage Grows
Being used as a crypto money mule can lead to frozen accounts, lost funds, and serious stress, especially if action is delayed. Criminals disappear, but victims are left dealing with the fallout.
In case of any suspicion that you are getting involved in a money mule scam, please cease and call Global Financial Recovery. Their crypto recovery team can be used to evaluate your situation, collaborate with financial providers, and assist you in the crypto money recovery process before the damage worsens.
FAQs (Frequently Asked Questions)
Scammers like crypto because transactions can move across borders in seconds and do not rely on a single bank or country. Public blockchains also let them layer and route funds through many wallets, which makes it harder for victims and investigators to follow the full trail in real time.
Yes, students and young professionals are often targeted because they are active online, may be looking for side income, and might not have much experience with financial crime risks. “Flexible” remote jobs and quick-profit crypto opportunities are designed to appeal specifically to this group.
In some cases, criminals use stolen IDs or documents collected through phishing or fake KYC requests to open wallets and exchange accounts in someone else’s name. Even if you did not move the funds yourself, your identity can be tied to suspicious activity, which is why protecting personal documents and selfies is critical.
Detection timelines vary widely: some patterns are flagged after the first suspicious transaction, while others go unnoticed until multiple victims report fraud or a major scam is exposed. The more complex the routing and the more platforms involved, the longer it can take for a clear picture to emerge.
That depends on the findings of the bank or exchange investigation. Some customers regain access after providing documentation and explanations, while others may face permanent account closures and difficulty opening new accounts elsewhere, which is why acting quickly and transparently is so important if you suspect a problem.




